NIST Cybersecurity Framework
Intro
The NIST Cybersecurity Framework (CSF) is a set of guidelines developed by the National Institute of Standards and Technology (NIST) to help organizations manage and reduce cybersecurity risk. It’s widely used across industries to improve cybersecurity posture in a structured and repeatable way.
Purpose of the NIST Framework:
Help organizations identify, manage, and reduce cybersecurity risks.
Provide a common language and structure for discussing cybersecurity.
Align cybersecurity activities with business requirements, risk tolerance, and resources.
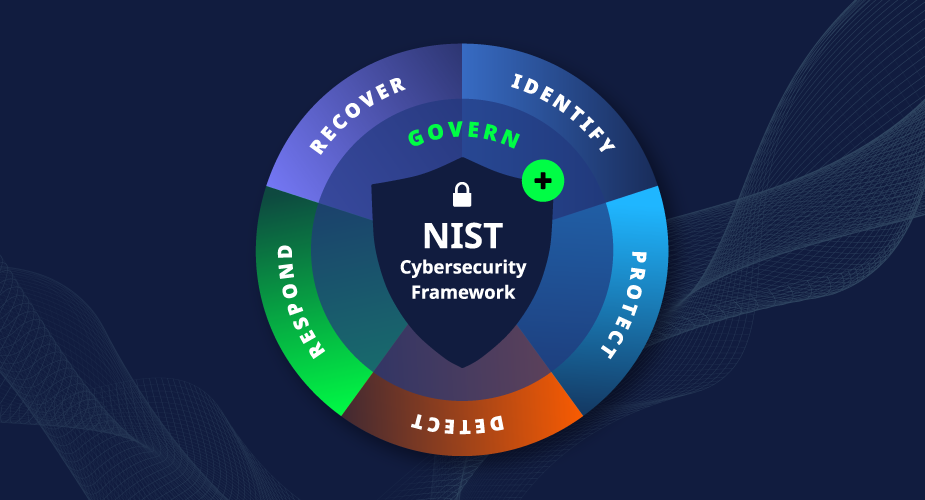
Phases of the NIST Framework:
Identify (Know assets & risks)
Purpose: Understand your organization’s environment to manage cybersecurity risk.
Includes: Asset management, business environment, governance, risk assessment, and risk management strategy.
Protect (Safeguards in place)
Purpose: Implement safeguards to limit the impact of potential cybersecurity events.
Includes: Access control, awareness training, data security, maintenance, and protective technologies.
Detect (Monitor & alert)
Purpose: Identify the occurrence of a cybersecurity event in a timely manner.
Includes: Anomalies and events, continuous monitoring, and detection processes.
Respond (Act on incidents)
Purpose: Take action regarding a detected cybersecurity incident.
Includes: Response planning, communications, analysis, mitigation, and improvements.
Recover (Get back to normal)
Purpose: Restore capabilities or services impaired due to a cybersecurity incident.
Includes: Recovery planning, improvements, and communications.
Real world example
Let’s say this company sells products online and handles customer payment data.
Identify
They map all digital assets (servers, databases, apps).
Assess which systems store customer credit card info.
Evaluate third-party vendors and compliance needs (e.g., PCI-DSS).
Protect
Implement firewalls, multi-factor authentication (MFA), and encryption.
Train employees on phishing awareness.
Regularly update software and monitor access control.
Detect
Use an Intrusion Detection System (IDS).
Set up alerts for suspicious login attempts.
Monitor logs for anomalies in data access patterns.
Respond
Create an Incident Response Plan (IRP).
When a breach occurs, activate IRP: isolate systems, notify affected customers, involve legal/PR teams.
Analyze the attack and how it happened.
Recover
Restore backups.
Patch vulnerabilities.
Update policies based on what was learned and conduct a post-incident review.